From your first
ghost account
to your SOC 2 report.
AutoCISO finds the access risks API tools can't see — then runs your entire compliance program until you're certified. One platform. From day one to audit day.
AutoCISO finds the access risks API tools can't see — then runs your entire compliance program until you're certified.
Run your first audit free →
Compliance has two problems.
Most tools solve neither.
Identity platforms see the federated half. GRC platforms automate the easy half. Real programs need both halves — and the work in between.
Problem 1
You can't see what you have.
Local admins. Unfederated SaaS. OAuth tokens. Service accounts.
Even with SSO, 30–40% of real access lives outside your IdP — and none of it shows up in an API export.
Problem 2
You can't run a program.
Policies, risk registers, internal audits, management reviews, evidence collection, auditor coordination.
The work of compliance — not just the tooling around it.
AutoCISO solves both — for companies with SSO and without.
From first audit to certificate, in one workspace.
Most platforms cover one slice of this path. AutoCISO walks the whole arc with you — and the same evidence that catches a ghost on day one feeds your auditor on day 180.
Day 1
Ghost Hunter audit
Upload one screenshot. See ghosts, zombies, license waste, and SOC 2 gaps in 5 minutes.
Week 1
Scope & gap analysis
AI-guided wizard maps your stack to ISO 27001 / SOC 2 and flags every control you're missing.
Week 2
Policies, risks, SoA
AI-drafted policies tailored to your stack. Live risk register with budget context. Statement of Applicability auto-generated.
Month 1
Access reviews & evidence
Quarterly reviews on autopilot. Evidence vault collects findings continuously, with chain-of-custody.
Month 3
Internal audit & management review
Built-in workflows. Auto-generated board packs. Readiness score climbs in real time.
Month 4–6
Auditor portal & certificate
Read-only auditor access. Pre-mapped evidence. You walk into the audit ready.
Sign into the live DEMO.
Right now. No form.
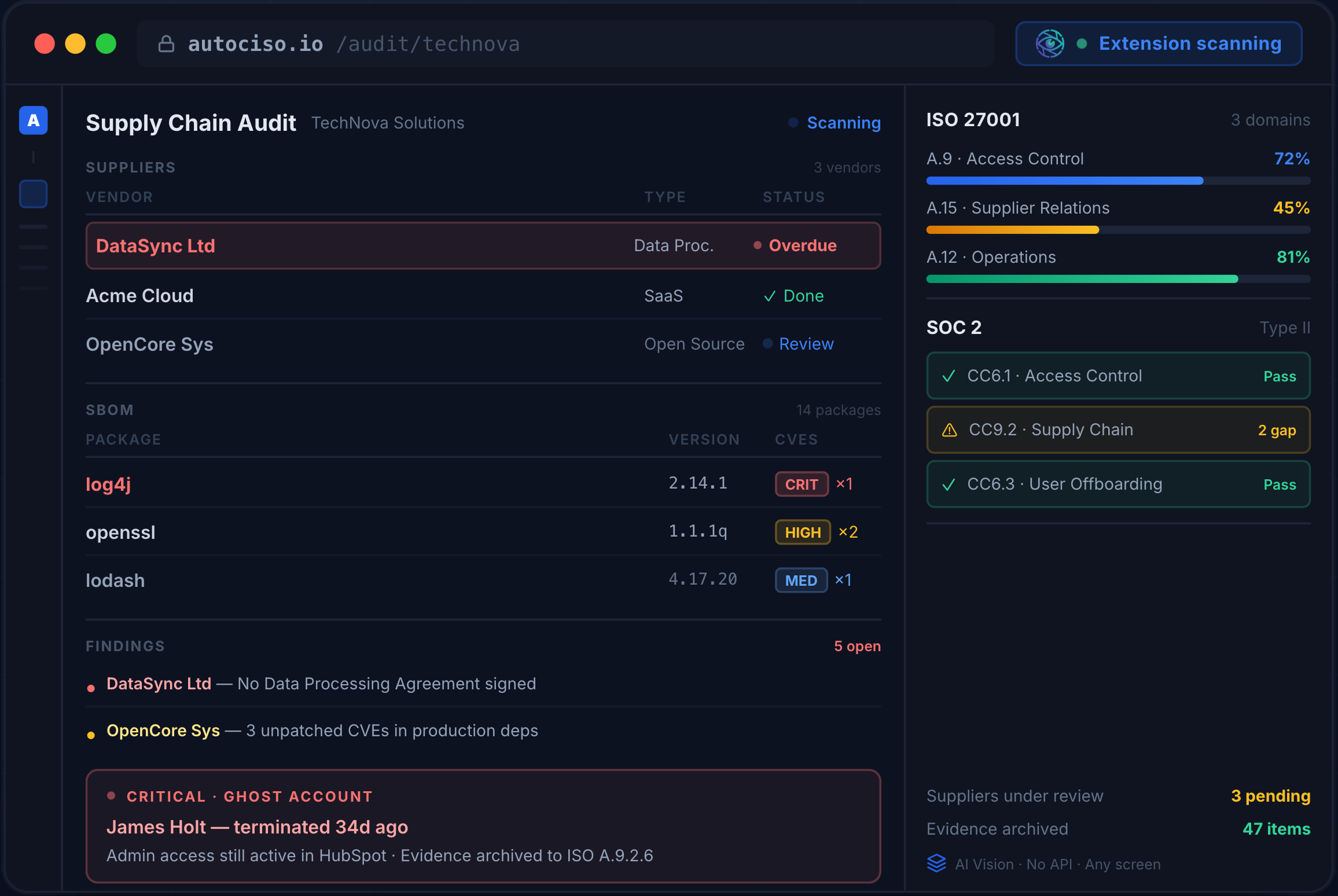
TechNova Solutions — a fictional 40-person SaaS company mid-way through ISO 27001. Real workflows, real anomalies, ghost accounts on a CRITICAL asset, two ISO projects side-by-side, and a vCISO workspace tracking month-over-month readiness. Resets fresh every night at 00:00 UTC.
Ghost account
on a CRITICAL asset
ISO 27001
2 projects, 70% live
AI risk interviews
3 sessions in flight
Supplier review
37 Qs · 3 findings
Offboarding gaps
3 unrevoked employees
vCISO workspace
readiness arc 42→79%
Two ways AI sees your stack.
One catches what other tools can't see. The other ingests everything else. You start with whatever you have. The graph grows with you.
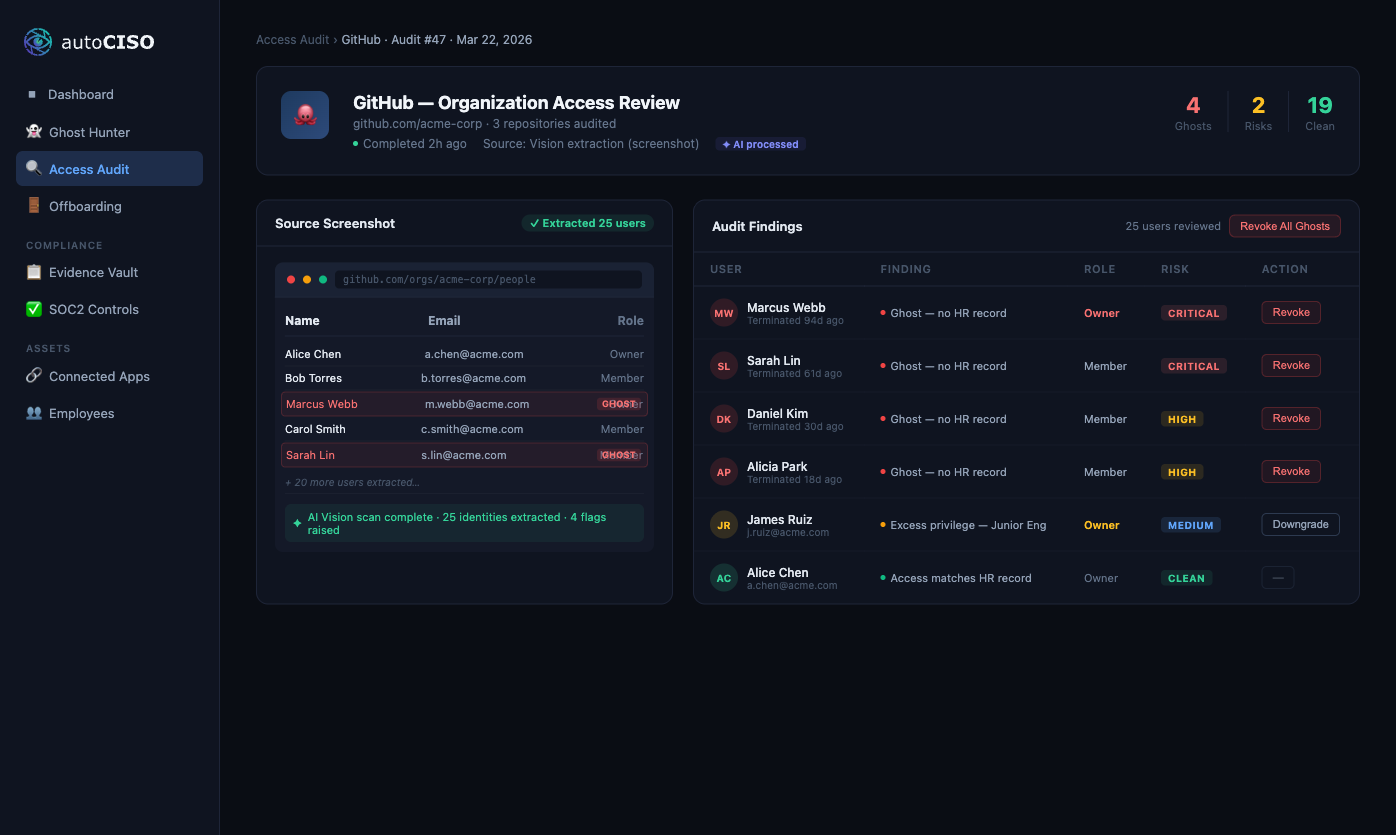
Vision
The input nobody else has
- ● Catches what APIs can't show: local admins, unfederated apps, cached sessions, OAuth integrations, service accounts.
- ● Even with Okta, 30–40% of real access lives outside SSO.
- ● Independent attestation layer — verifies what your IdP claims.
API + SCIM + CSV
The inputs everyone has
- ● Native connectors for major SaaS.
- ● HRIS sync as ground truth for identity reconciliation.
- ● Hybrid identity graph blends every source into one view.
If you can see it on a screen,
we can audit it.
Other platforms build API connectors. We build Eyes. That covers 100% of your apps — not just the 800 with integrations.
Upload
Take a screenshot of any app's "Users" page — or let the browser extension capture it automatically.
Extract
AI Vision identifies every user, role, email, and status. No API needed. No integration required.
Match
Fuzzy identity matching cross-references the list against your HR system or employee CSV.
Flag
Discrepancies surface as risks: ghost accounts, zombie licenses, privilege mismatches, service accounts.
Act
One click creates Jira or Slack tasks for asset owners. Evidence is archived for your auditor.
One platform. Three jobs. Zero spreadsheets.
Not a utility. Not a checklist. The full virtual-CISO scope, organized around the work of running a real program.
Access Intelligence
See every account, owner, and ghost — including the ones APIs miss.
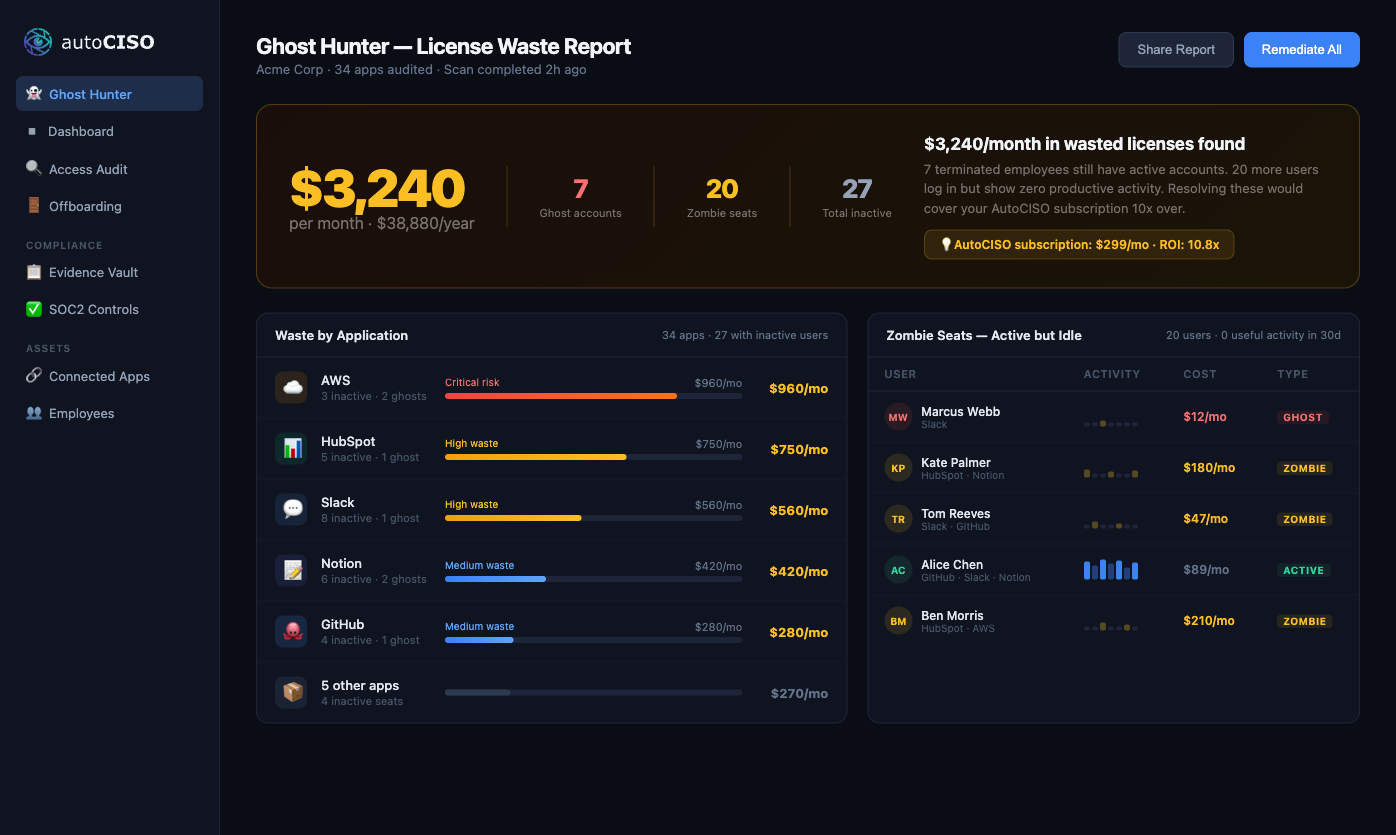
- Ghost Hunter
- License Waste Calculator
- Zombie Hunter
- Offboarding Command Center
- Periodic Access Reviews
Compliance Program
Run the actual work of compliance, not just the tooling.
- Scope Wizard
- AI Policy Generator
- Risk Management Workspace
- Internal Audit
- Management Review
- Evidence Vault
Audit & Certification
Walk into the audit with evidence already mapped to controls.
- Auditor Portal
- Readiness Score
- Continuous Evidence
- SOC 2 + ISO 27001:2022 + HIPAA control mapping
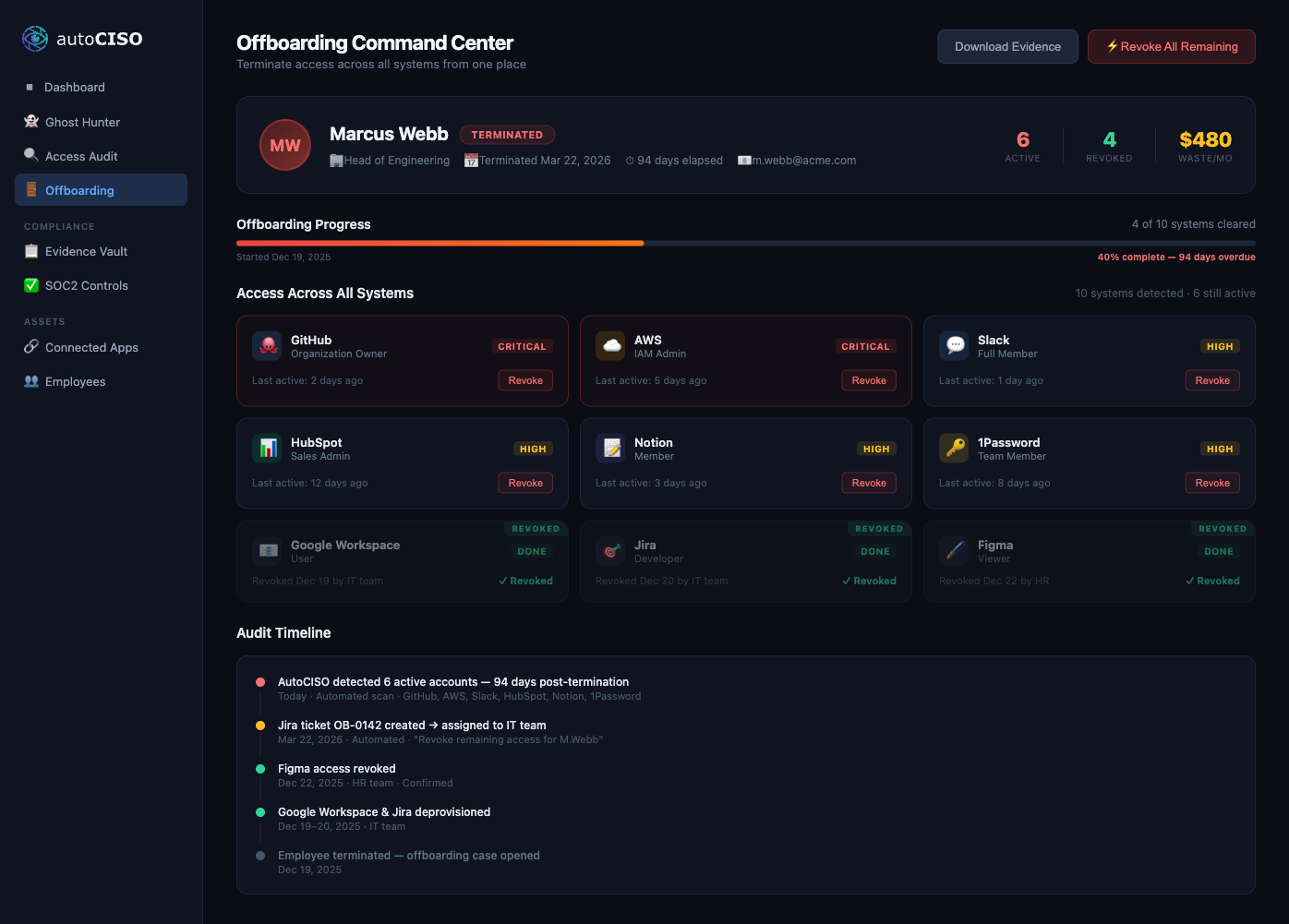
Automated Offboarding without SSO:
The moment you let someone go, the clock starts ticking.
The average company takes 4–6 weeks to fully revoke a terminated employee's access — if they ever do. Meanwhile, that person can still log in, download data, and run up your licensing bill.
- ✓ Detect all active access across every audited app in minutes
- ✓ One-click generates revocation tasks in Jira and Slack
- ✓ Full audit timeline archived as SOC2 evidence
- ✓ Progress tracker shows which systems are still open
SOC2 evidence in hours.
Not weeks of spreadsheets.
The average SOC2 audit prep takes 40+ hours of manual screenshot collection. AutoCISO automates the collection, structures the evidence, and flags the gaps — before your auditor sees them.
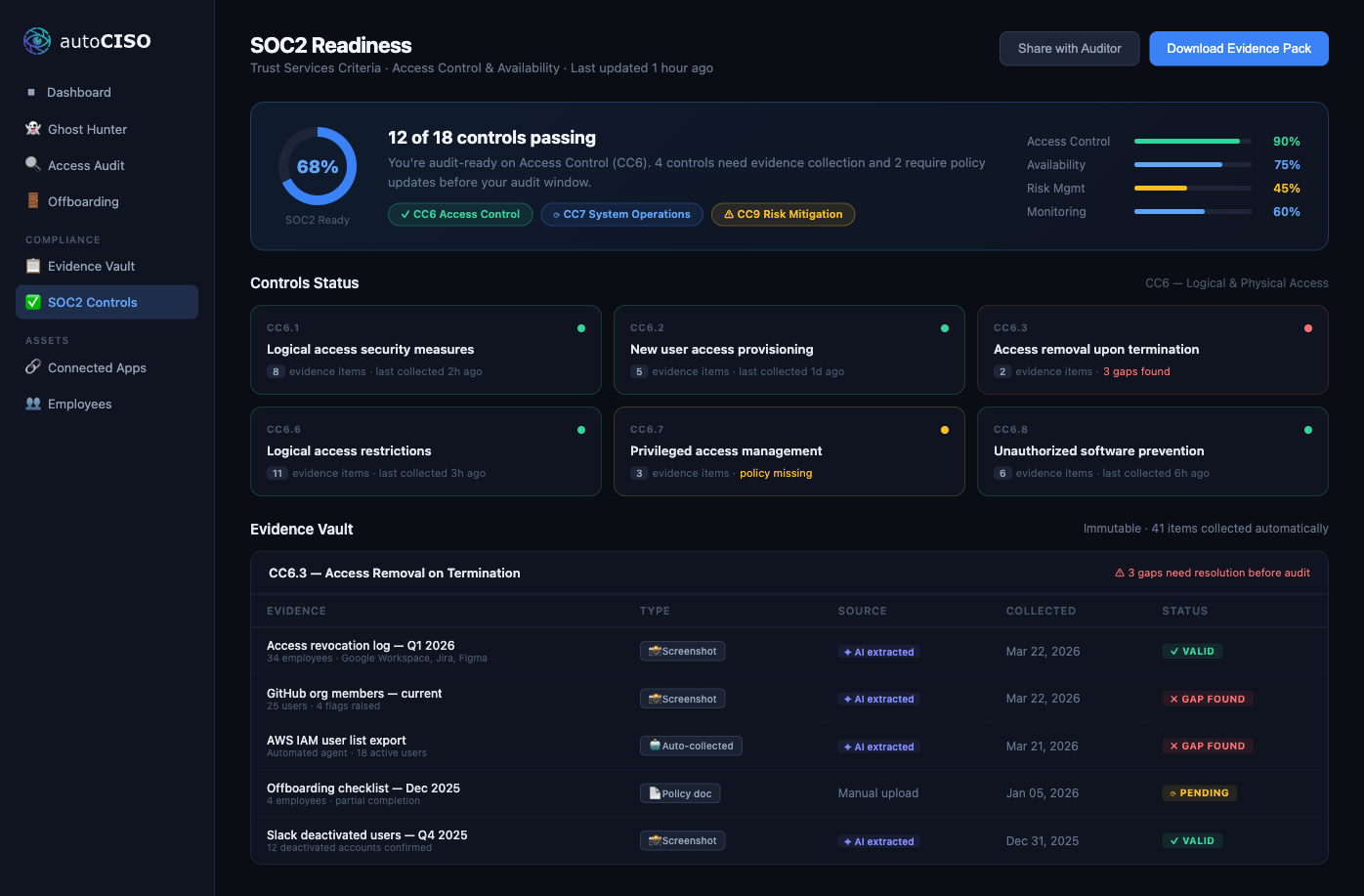
Auto-collects access evidence across all connected apps
Maps findings directly to SOC2, ISO 27001, and HIPAA controls
Immutable evidence vault with AI extraction audit trail
"Audit Simulator" mode stress-tests your program pre-audit
Already have Okta?
You're not done.
SSO covers your federated apps. AutoCISO covers everything else — the apps that never federated, the local admins your IdP can't see, the OAuth tokens that survive deactivation, the service accounts nobody owns.
Your auditor will ask about all of them. AutoCISO has the evidence.
Continuous attestation
Vision verifies what API and SSO claim — independent evidence your auditor will trust.
Shadow IT discovery
Browser extension finds unfederated SaaS your IdP never sees.
M&A due diligence
Every acquired company starts as screenshots — no waiting for IT integration.
Subsidiary mode
Audit subsidiaries that don't share your IdP without forcing a tenant migration.
Built for the people security tools forgot.
CTO / VP Engineering
10–30 person startup
"We just fired our Head of Sales and I realized he still has access to HubSpot, Stripe, and our AWS staging environment."
Goal: Peace of mind and a defensible offboarding process.
Head of Operations
40–80 person company
"The SOC2 auditor is here in 3 weeks and I'm manually pulling screenshots of every app's user list."
Goal: Automated evidence collection and a repeatable process.
VP Security
80–150 person company
"Enterprise customers won't sign until we can show compliance. We can't afford to hire a 5-person security team."
Goal: A full CISO office without the headcount.
Head of Security
150–500 person scale-up
"We have SSO, but our auditor keeps finding access we don't track. We need verification, not another integration list."
Goal: Independent attestation that closes the gap between the IdP and reality.
Virtual CISO
MSP managing 5–20 clients
"I need to run access audits across all my clients without switching between 20 different portals."
Goal: Centralized multi-client dashboard and white-labeled reports.
AutoCISO vs. Everyone Else
| Dimension | AutoCISO | Everyone Else |
|---|---|---|
| Coverage model | Vision-first, API-augmented | API-only — limited coverage |
| Lifecycle scope | Audit → Program → Certificate | One slice (evidence or identity) |
| Setup time | 5 minutes | Days to weeks |
| Legacy & unfederated apps | Yes — if you can see it | No |
| Independent attestation | Verifies what API/IdP claims | Trusts the API |
| Target market | SMBs through 500-person scale-ups | Enterprise-only or SMB-only |
| ROI model | Pays for itself month one | Pure cost center |
Insights for the SSO-less era
Technical guides and strategic playbooks for securing modern SaaS sprawl.
How to Automate Evidence Collection Without API Connectors
Manual audit evidence is slow, stale, and expensive. Here is a practical playbook to automate evidence collection across both API-friendly and non-integrated apps.
Unified Control System for Continuous Compliance
AutoCISO's Unified Control System replaces annual audit prep with continuous compliance: one engine, many frameworks, shared evidence, live posture scoring.
Your Suppliers Are Inside Your Security Perimeter (Whether You Track Them or Not)
Supplier risk is not a procurement concern. It is an operations problem — and most growing companies do not discover that until audit season.
Start with one screenshot. End with a certificate.
Free audit. No credit card. No integrations. 5 minutes. Then we'll take it from there.