Continuous compliance has been talked about for years, but most teams still run annual audit projects. They spin up a tracker before ISO 27001, SOC 2, or customer due diligence deadlines, collect a large pile of evidence, pass the checkpoint, and then drift back into reactive mode.
That pattern is expensive, and for small security teams it is exhausting. It is also avoidable.
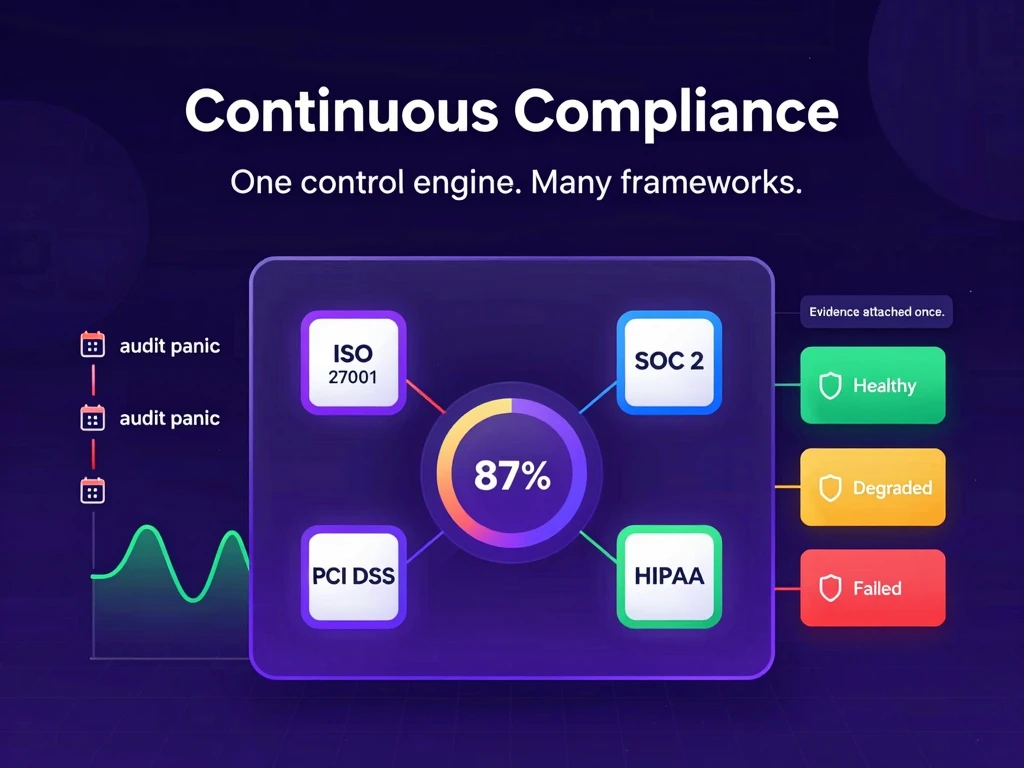
Today we are launching AutoCISO’s Unified Control System: one control engine built to support multi-framework compliance without forcing you to rebuild your workflow for each framework.
The problem: fragmented frameworks, duplicate evidence, annual panic cycles
If you have lived through back-to-back audit cycles, this will sound familiar.
You build controls for ISO 27001. Then a customer asks for SOC 2 alignment. Then PCI DSS shows up in sales conversations, or HIPAA appears because your product moves into healthcare workflows. The underlying security work is often similar, but the operating model is not. Most teams end up with parallel trackers, framework-specific spreadsheets, and different evidence folders for what is often the same control intent.
A single access review can become four separate documentation tasks:
- One file for ISO
- One file for SOC 2
- One file for PCI
- One file for internal review notes
None of that reduces risk. It just increases administrative overhead.
For SMEs with one or two people covering security and compliance, this approach does not scale. You do not have a spare GRC department. You have to run security operations and prove control effectiveness with the same limited bandwidth.
Annual compliance cycles create another issue: blind time between audits. A control that looked fine three months ago can degrade quietly. Evidence expires. Exceptions remain open without deadlines. Ownership changes and nobody updates the review cadence. The next time this becomes visible is often when an auditor asks a direct question.
Compliance should not work like a fire drill.
The solution: one control engine, many frameworks
The Unified Control System changes the center of gravity from framework checklists to framework-agnostic control objectives.
Instead of treating every framework control as a separate work item, we define the objective first. Then we map framework control references to that objective through a crosswalk model.
That means your team does this once:
- Define or adopt the control objective.
- Attach evidence to the objective.
- Track control health and exceptions at the objective level.
- Reuse that objective context across mapped frameworks.
Not this:
- Repeat the same process per framework.
- Maintain separate evidence trails for each audit lens.
- Reconcile differences manually every quarter.
Production today includes broad objective coverage and crosswalk mappings for ISO 27001 and SOC 2, with PCI DSS and HIPAA mappings available as expanding beta sets. The architecture is the key: new frameworks are onboarded by extending mappings, not by rebuilding your compliance operations.
If you want context before diving into the details, the approach aligns with how we think about operational security programs across risk management use cases and SOC 2 readiness workflows.
What this changes in daily work
The launch is not a single widget. It is a connected operating model made of several shipped capabilities.
1) A unified posture view, not scattered snapshots
The Compliance Cockpit provides one posture score with dimensional breakdown across controls, evidence freshness, risk, and supplier posture. You can see how the score moves over time and where degradation is happening, instead of stitching together separate module views.
For practical operations, that means your weekly review starts with one screen and one priority queue.
2) Shared evidence across mapped controls
Evidence now follows objectives. When an artifact supports a mapped objective, it contributes to all linked framework controls for that objective instead of living as duplicate uploads in multiple framework buckets.
Your team spends less time renaming files and more time closing gaps.
3) Reliability states for controls
Controls are not binary forever-pass items. They are healthy until they are not.
Reliability scoring introduces state tracking so controls can move through healthy, degraded, failed, or unknown based on freshness and linked signals. This gives teams an operational language to discuss control quality and recovery speed, not just audit status.
4) Exception SLA tracking with accountability
Exceptions are part of real compliance programs. The issue is unmanaged exceptions that never close.
Time-bound exception handling with SLA windows creates explicit ownership and deadlines. Exceptions are linked to risk decisions, and overdue exceptions are visible instead of hidden in informal notes.
5) Framework export packs without rebuild work
When you need auditor-ready output, export packs generate framework-specific evidence bundles and control matrices from current platform state. You are exporting from a live system, not assembling a one-off package from scratch.
6) AI support tied to live compliance data
The AI assistant can answer operational questions against current compliance context, for example:
- “Which controls are currently failing?”
- “Show me overdue compliance exceptions.”
- “What is the SOC 2 equivalent for this ISO control?”
That is different from static guidance. It is workflow support for active programs.
Practical walkthrough: one access review, multiple proofs
Consider a recurring access review process.
Your team runs a quarterly review for privileged access. The review produces one artifact package: reviewer approvals, revoked access actions, and timestamped evidence of completion. In the Unified Control System, that artifact is attached to the objective “Access rights are provisioned and reviewed.”
From there, crosswalk mappings determine framework coverage.
In current live mappings, that objective aligns directly to:
- ISO 27001 A.5.18
- SOC 2 CC6.2
- SOC 2 CC6.5
In the expanding beta mapping set, the same objective is also aligned for:
- PCI DSS 7.2
- HIPAA 164.312(a)(1)
The operational outcome is the same direction you want long term:
- One objective workflow
- One evidence collection motion
- Multi-framework traceability
No parallel trackers. No manual evidence cloning. No separate reconciliation exercise right before each audit event.
What is new in this launch
Here is the concrete scope now available in the Unified Control System release:
- Compliance Cockpit with unified posture score, dimensional breakdown, coverage matrix, and trend visibility
- Crosswalk Engine with framework-agnostic objectives and bidirectional control lookup
- Shared objective-linked evidence so one evidence stream supports mapped controls
- Continuous control reliability states with degradation and failure visibility
- Exception SLA management for time-bound exceptions tied to risk decisions
- Framework export packs to generate audit-ready outputs from live data
- AI compliance assistant workflows for control reliability and crosswalk questions
Framework coverage status is transparent:
- ISO 27001 + SOC 2: strongest and most complete mapping coverage today
- PCI DSS + HIPAA: active beta mapping expansion
We consider this important to state explicitly. Multi-framework trust comes from accurate coverage statements, not broad claims.
Why this matters for SME security teams
Large enterprises can hide process inefficiency behind staffing. SME teams cannot.
If you are running compliance with a lean team, your limiting factor is not usually security knowledge. It is operational throughput.
The Unified Control System is designed to improve that throughput:
- Reduce duplicate work by moving evidence to objective level
- Improve signal quality through reliability states
- Reduce “audit season panic” by keeping controls continuously visible
- Make exceptions explicit and time-bound
- Keep exports close to real-time readiness
This is also a better communication model for leadership and partners. A posture trend plus reliability state distribution is a clearer narrative than a stack of spreadsheets and point-in-time checklists.
How to use it now
If you are already in AutoCISO, start with this sequence:
- Open your compliance cockpit and review the dimensional score breakdown.
- Inspect objective mappings for your priority controls in crosswalk explorer.
- Attach evidence at the objective level wherever possible.
- Review failed and degraded controls first, then address overdue exceptions.
- Generate a framework export pack to validate audit-readiness quality.
If you are evaluating the model and want the broader platform flow, the How It Works page and our access review use case show the surrounding operational context.
Annual audit prep is not going away as a requirement. But annual-only compliance operations are optional.
The Unified Control System is our move from static compliance projects to a living control system that can keep pace with how modern teams actually ship and operate.