Three ways AI sees your stack.
One identity graph.
Vision picks up what APIs can't show. APIs sync where they exist. CSV and HRIS fill the rest. AutoCISO turns all three into a single source of truth — and feeds it straight into your compliance program.
API integrations are great —
when they exist and tell the truth.
Even with Okta, 30–40% of real access lives outside what your IdP can see. APIs cache, lag, mis-map roles, and miss permissions that live one UI layer deeper.
What APIs can't show you:
- → Local admins created outside your IdP
- → OAuth tokens that survive employee deactivation
- → Service accounts that nobody owns
- → Cached sessions still logged in 6 months later
- → Unfederated SaaS your team signed up for last week
- → "Read-only" roles that quietly include export permissions
Vision sees the screen the way your auditor will. That's independent attestation — no API-first tool can do it.
| Capability | Vision | API / SCIM | CSV / HRIS |
|---|---|---|---|
| Local admins outside IdP | ✓ | — | — |
| OAuth tokens & integrations | ✓ | partial | — |
| High-frequency sync | — | ✓ | — |
| IdP-federated apps | opt | ✓ | — |
| Source of truth (employees) | — | — | ✓ |
| Legacy / on-prem systems | ✓ | — | ✓ |
| Independent attestation | ✓ | — | — |
AutoCISO uses all three. None of them is enough alone.
Three lanes in. One identity graph out.
Lane A — Vision
The unique one. Sees what APIs can't.
- 01
Capture
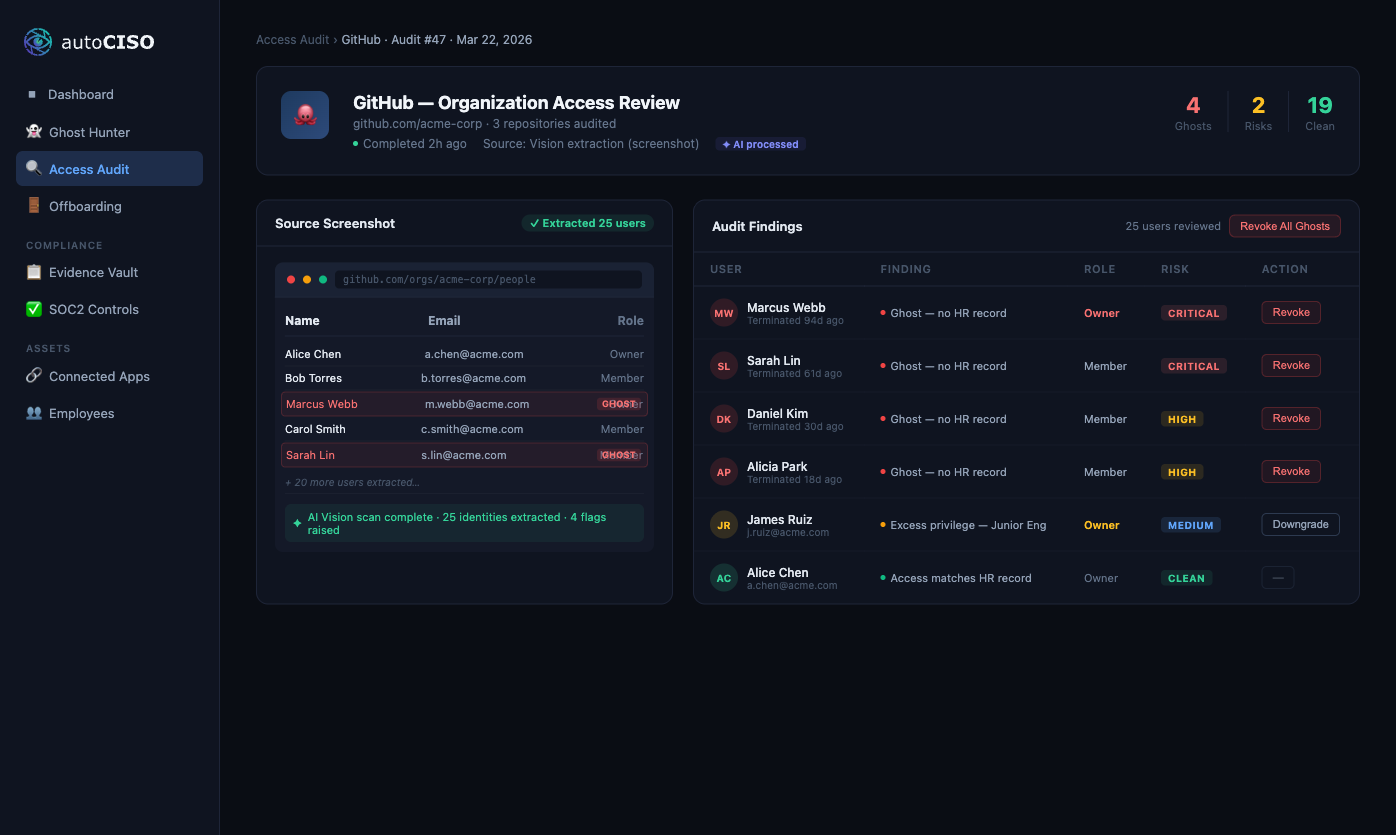
Take a screenshot of any app's "Users" or "Members" page. Or install the Legacy Bridge browser extension for one-click capture from any tab.
- 02
Pre-process
The image is run through a local PII masking pipeline. Names and emails are tokenised before any data leaves your environment. Raw PII never reaches an LLM.
- 03
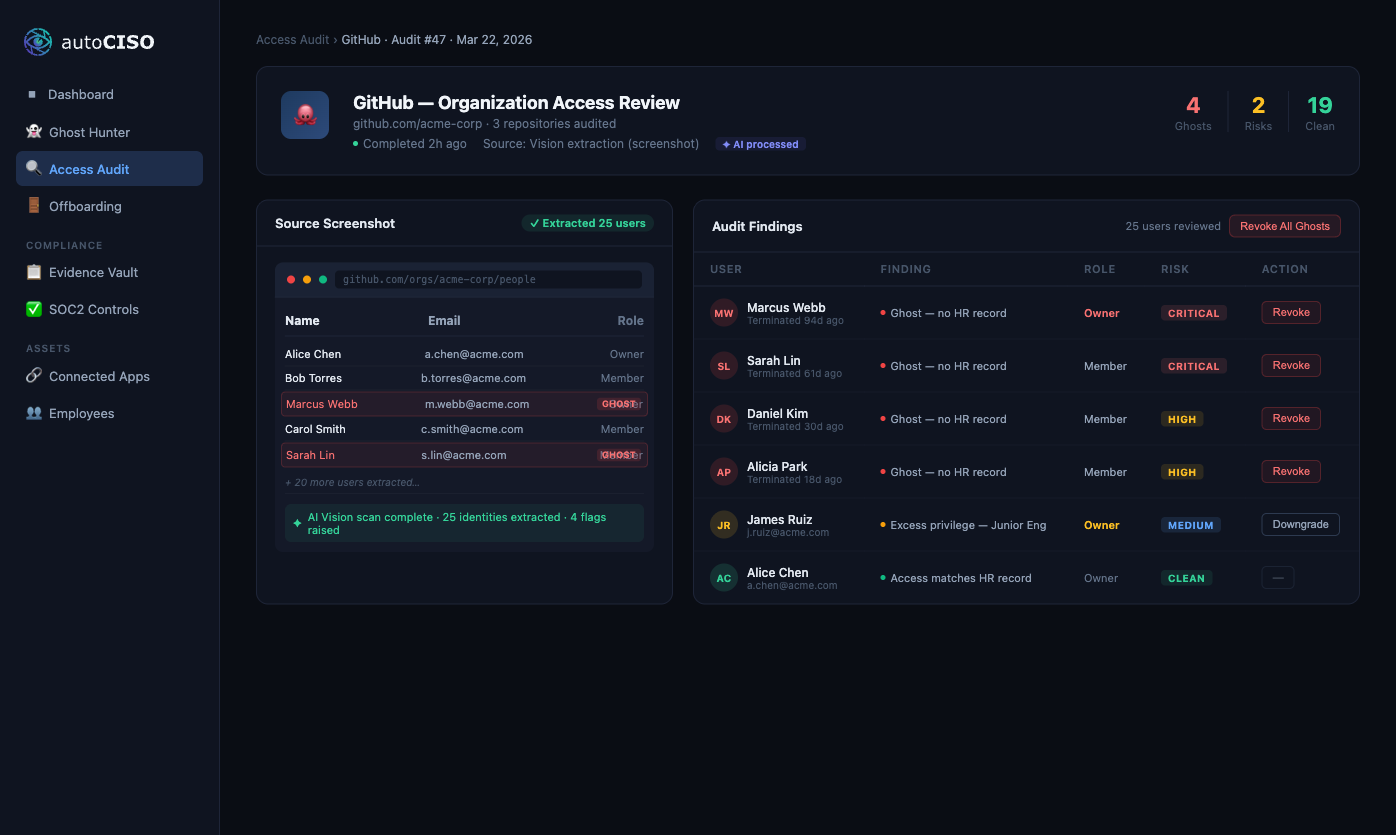
AI Vision Extraction
GPT-4o Vision and Claude Vision read the masked image and extract a structured user list: names, emails, roles, statuses — exactly as they appear on screen.
- 04
Fuzzy Identity Matching
Extracted identities are matched against your HR system or employee CSV using Levenshtein distance and email normalisation. "M. Webb" maps to "Marcus Webb" maps to m.webb@acme.com.
- 05
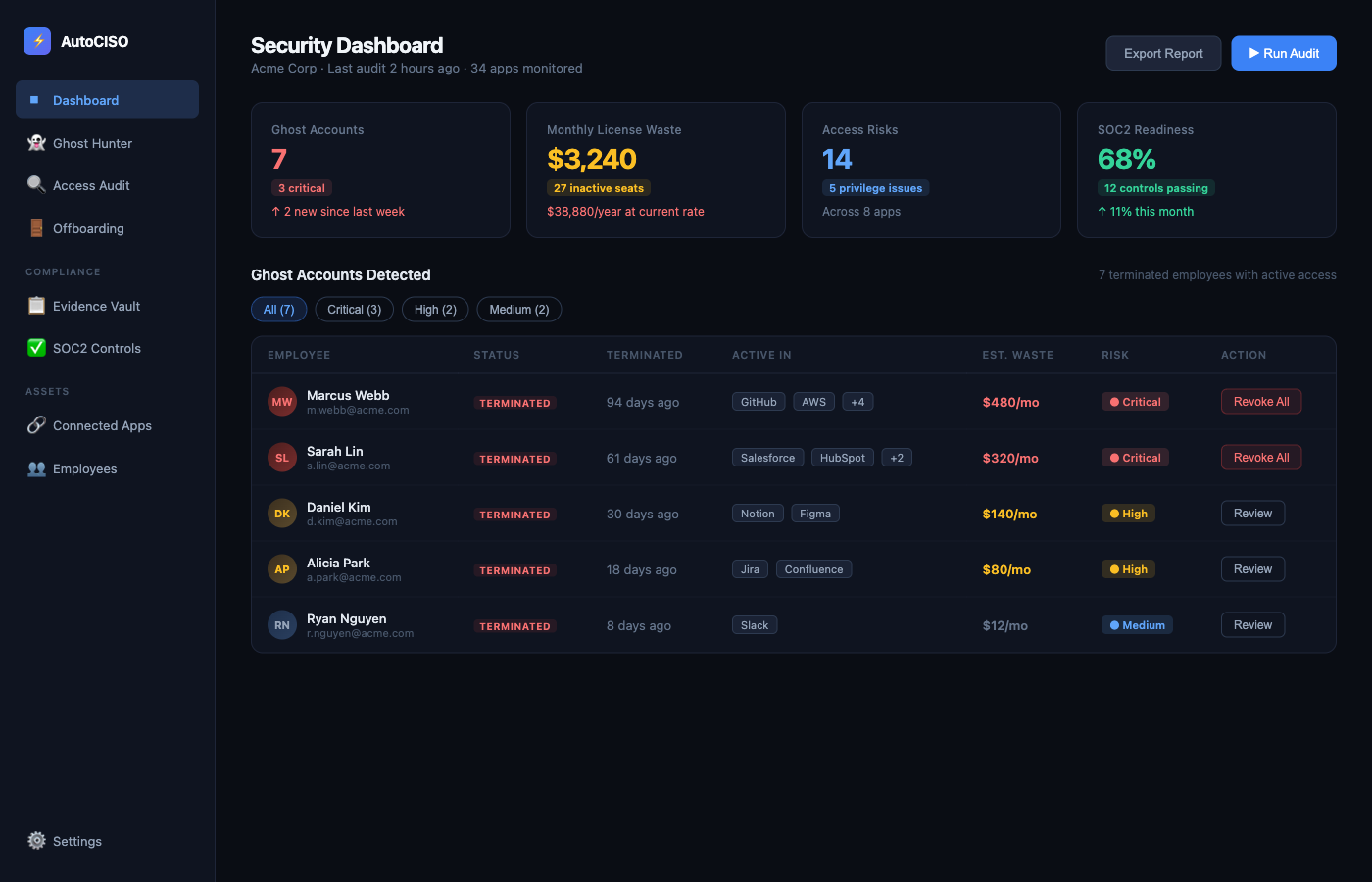
Risk Classification
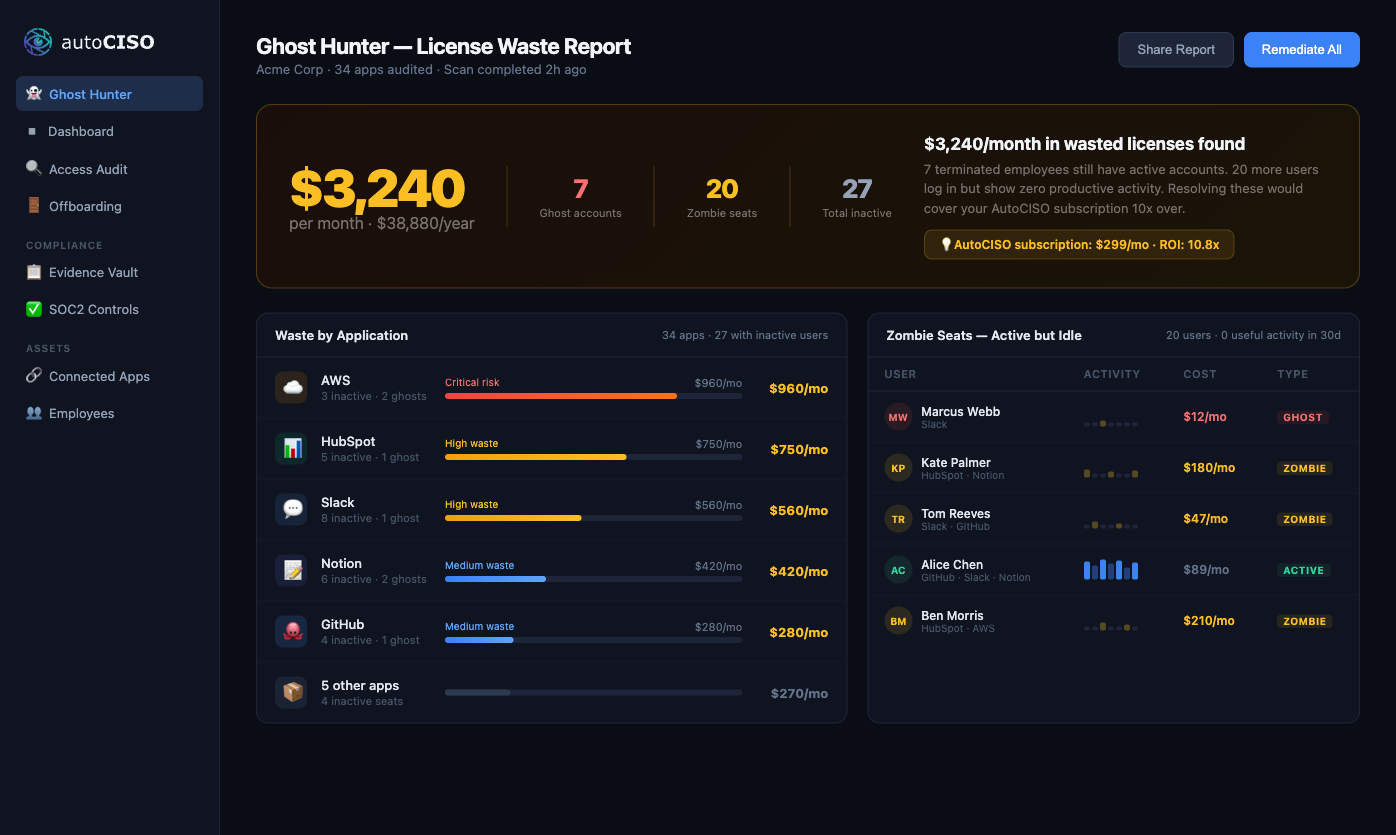
Unmatched users are classified as ghost accounts. Matched-but-inactive users become zombie seats. Privilege escalations and toxic combinations are scored and ranked.
- 06
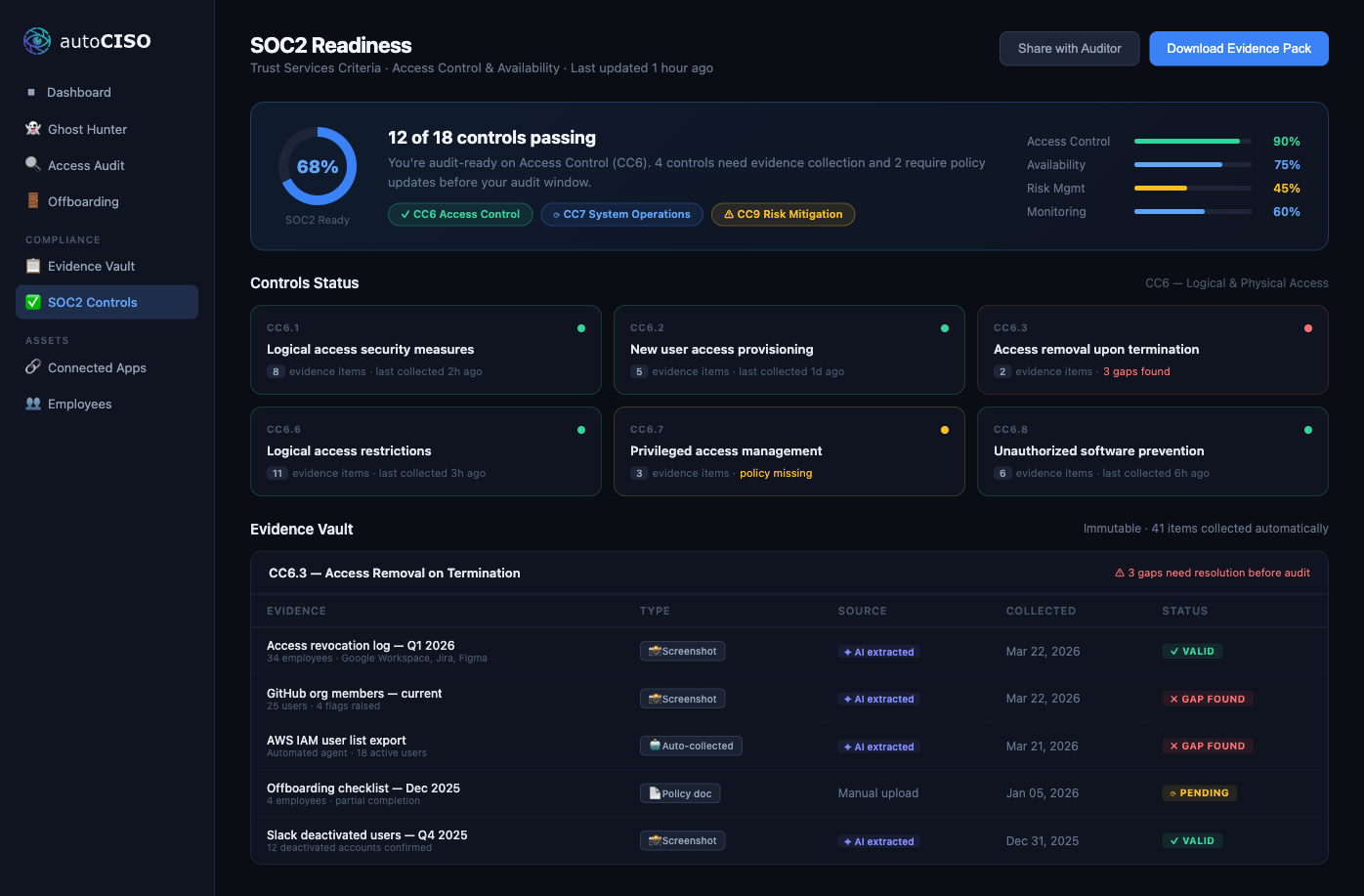
Evidence Archive
Every finding is linked to the source screenshot, the extracted data, and the matching decision. Immutable evidence chain — ready for your SOC2 auditor.
Lane B — API & SCIM
When available. Fast, standard, well-understood.
Native connectors for major SaaS platforms sync continuously. SCIM pulls from your IdP for federated apps. Standard, high-frequency, reliable — where it exists.
Lane C — HRIS & CSV
The ground truth for who is actually employed.
Your HRIS is the authoritative source for employment status. CSV imports cover custom, legacy, and on-prem systems. This is the baseline everything else is reconciled against.
Reconciliation Engine
All three lanes flow into fuzzy identity matching, role normalisation, and conflict detection. One identity graph. One risk model. One evidence chain.
Vision verifies what your API claims.
APIs lie. Not maliciously — they cache, lag, mis-map roles, and miss permissions that live one UI layer deeper. AutoCISO runs both. The API says one thing. Vision sees what's actually rendered to a logged-in admin. Mismatches become findings.
Example mismatch
- → Logged as control-effectiveness gap. Linked to SOC 2 CC6.1.
- → Auditor-ready evidence with both data sources side by side.
This is independent attestation. No API-first tool can do it.
Findings don't sit in a dashboard.
They run your program.
Every finding from the pipeline flows into a full compliance lifecycle. The pipeline is the start. The lifecycle is the product.
Risk Management Workspace
Risks scored, owned, and budgeted. Context from every audit. Live register, not a spreadsheet.
Evidence Vault
Chain-of-custody for every artifact. Source screenshot, extracted data, matching decision — immutable.
Access Reviews
Quarterly review campaigns on autopilot. Certify, revoke, escalate — all in one flow.
Internal Audit
Built-in audit workflows, not spreadsheets. ISO 27001, SOC 2, custom frameworks.
Auditor Portal
Read-only access for your external assessor. Evidence packages, not email threads.
AI CISO Copilot
Interprets findings, writes remediation plans, drafts policies. Your AI security lead.
Your employees' data never leaves your environment unmasked.
Local PII Masking
Names, emails, and roles are tokenised on your machine before any API call. The AI sees masked tokens, not real identities.
Encrypted Credential Storage
All credentials and secrets are encrypted with AES-256-GCM before storage. Zero plaintext secrets — ever.
Supply Chain Security
Third-party dependencies are matched against the NVD vulnerability database. Known CVEs are surfaced before they reach production.
Immutable Audit Trail
Every AI extraction is linked to its source screenshot. Chain-of-custody maintained for your SOC2 auditor.
Start with one screenshot. End with a certificate.
Free audit. No credit card, no integrations, 5 minutes. Then we'll take it from there.