Most growing companies do not fail at risk management because they cannot see risk.
They fail because they cannot operationalize it.
Someone notices that privileged access keeps surviving role changes. Someone else worries that backups have never been restored under pressure. A third stakeholder points out that contractors still export customer data to unmanaged laptops.
All of those are real risks. None of them automatically becomes a useful risk record.
That conversion step is where most programs break.
The classic risk register problem
The traditional model assumes the organisation has a small number of people who know how to speak fluent risk-management language. Everyone else is expected to hand over their concerns and wait for translation.
That creates three predictable failures.
First: intake becomes expert-only. Team leads and operators often have the best situational awareness, but they do not want to complete a heavyweight expert form every time they notice a real issue. So they delay. Or they send a Slack message. Or they mention it in a meeting and assume someone else will formalise it later.
Second: the register becomes static. Even when risks do make it into a spreadsheet or a GRC tool, they often arrive detached from the context that made them important in the first place. After a few weeks, the register turns into a list of stale sentences rather than a live operating view.
Third: treatment decisions get separated from financial reality. A risk can be scored, discussed, and escalated without ever answering the practical question leadership actually needs: what does it cost to reduce this, what happens if we do not, and which decision fits this quarter?
That is why so many risk registers exist without driving action.
A risk program needs more than a form
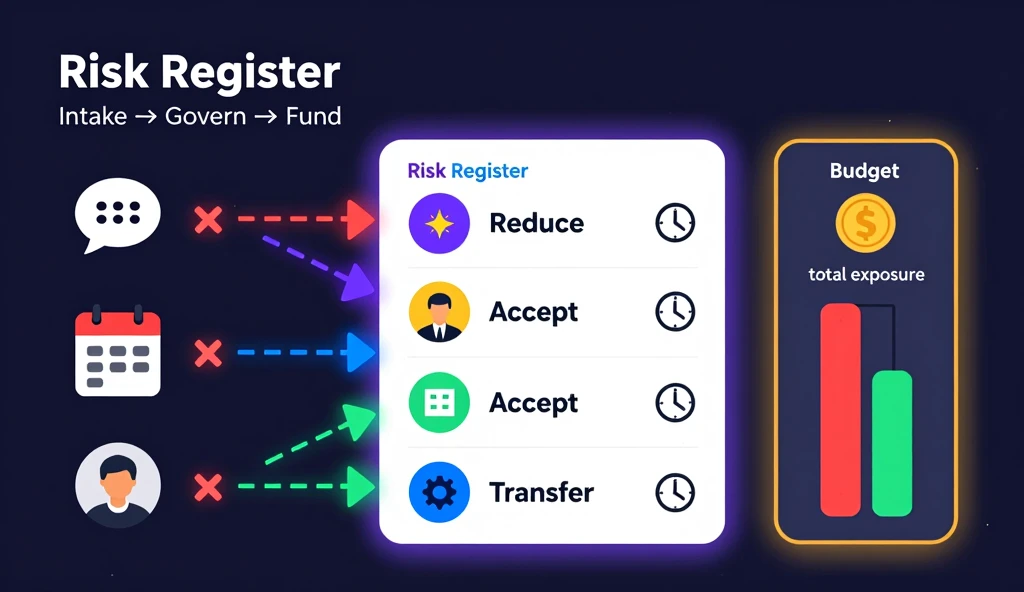
A working program needs at least four layers:
- a way for non-experts to contribute useful input
- a way for experts to refine and govern the record
- a shared register that stays current after intake
- a treatment view that connects priority to available budget
If any one of those layers is missing, the process starts to collapse back into side conversations, spreadsheets, and one-off workshops.
That is the operating gap the new Risk Management Workspace in AutoCISO is designed to close.
Start where the stakeholder is, not where the framework starts
One of the biggest mistakes in risk tooling is assuming everyone should begin with the same surface.
A founder, engineering manager, and compliance lead do not think about risk the same way. They should not have to.
AutoCISO’s new risk module supports three entry modes that all write into the same canonical model:
- AI-guided interview for people who can describe the reality but do not want to navigate formal terminology
- Quick form for teams that already understand the problem and want a fast path into a structured draft
- Expert editor for risk managers who want direct control over scoring, ownership, and treatment fields
That matters because the point of a risk program is not to force everyone into one ritual. The point is to capture good signal from the business and make it governable.
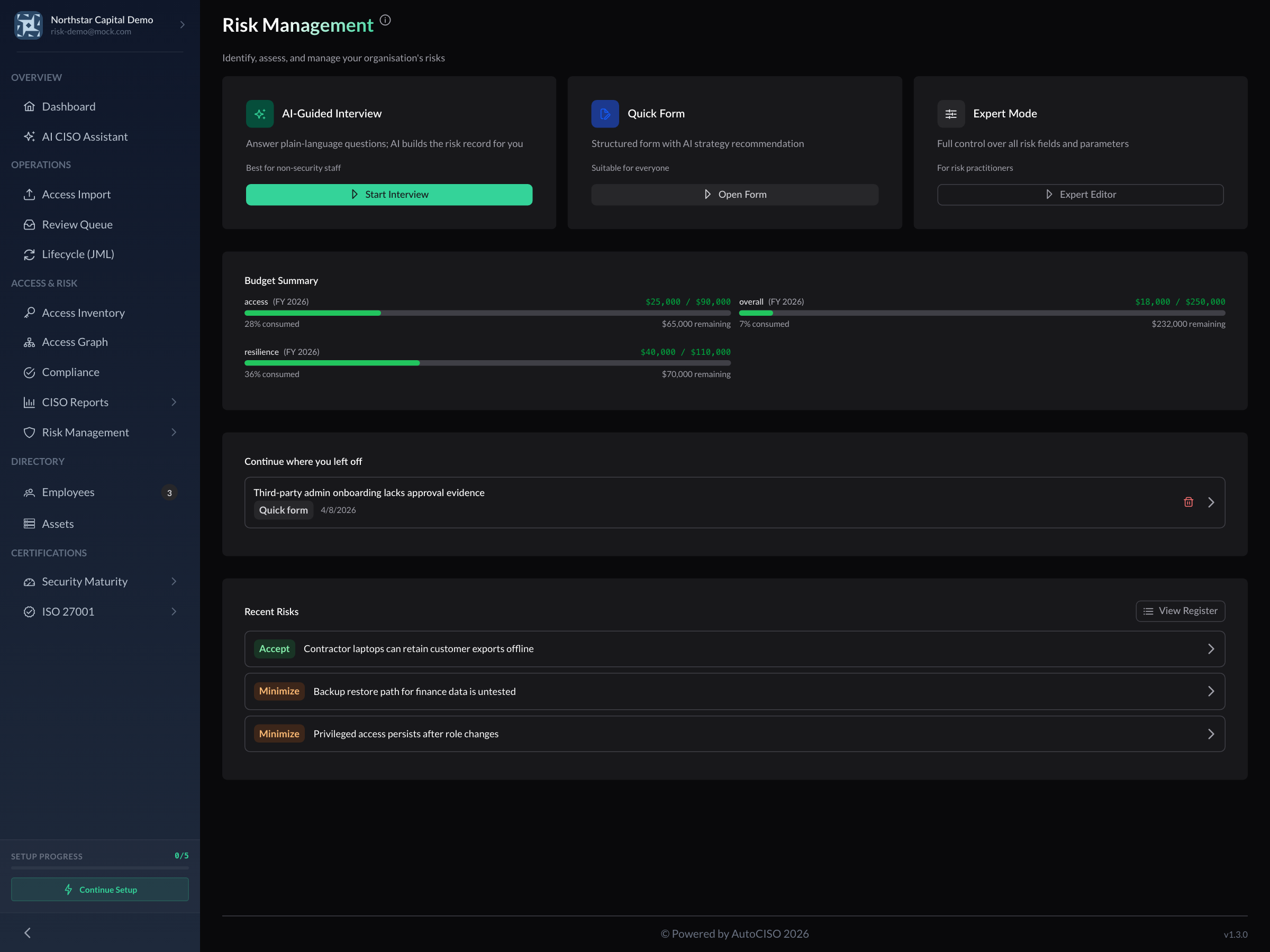
The workspace gives teams three ways in without fragmenting the underlying register.
The register has to become an operating surface
A risk record is useful only if people return to it.
That means the register cannot be a dead-end document. It has to support filtering, ownership, review dates, strategy status, and enough structure to answer practical questions during weekly operations:
- Which domains are driving the most exposure right now?
- Which risks are still active?
- Which ones were accepted temporarily rather than reduced?
- Who owns the next review?
The new AutoCISO register is built around that operational view. Risks can be segmented, filtered, and revisited without losing the intake history that created them.
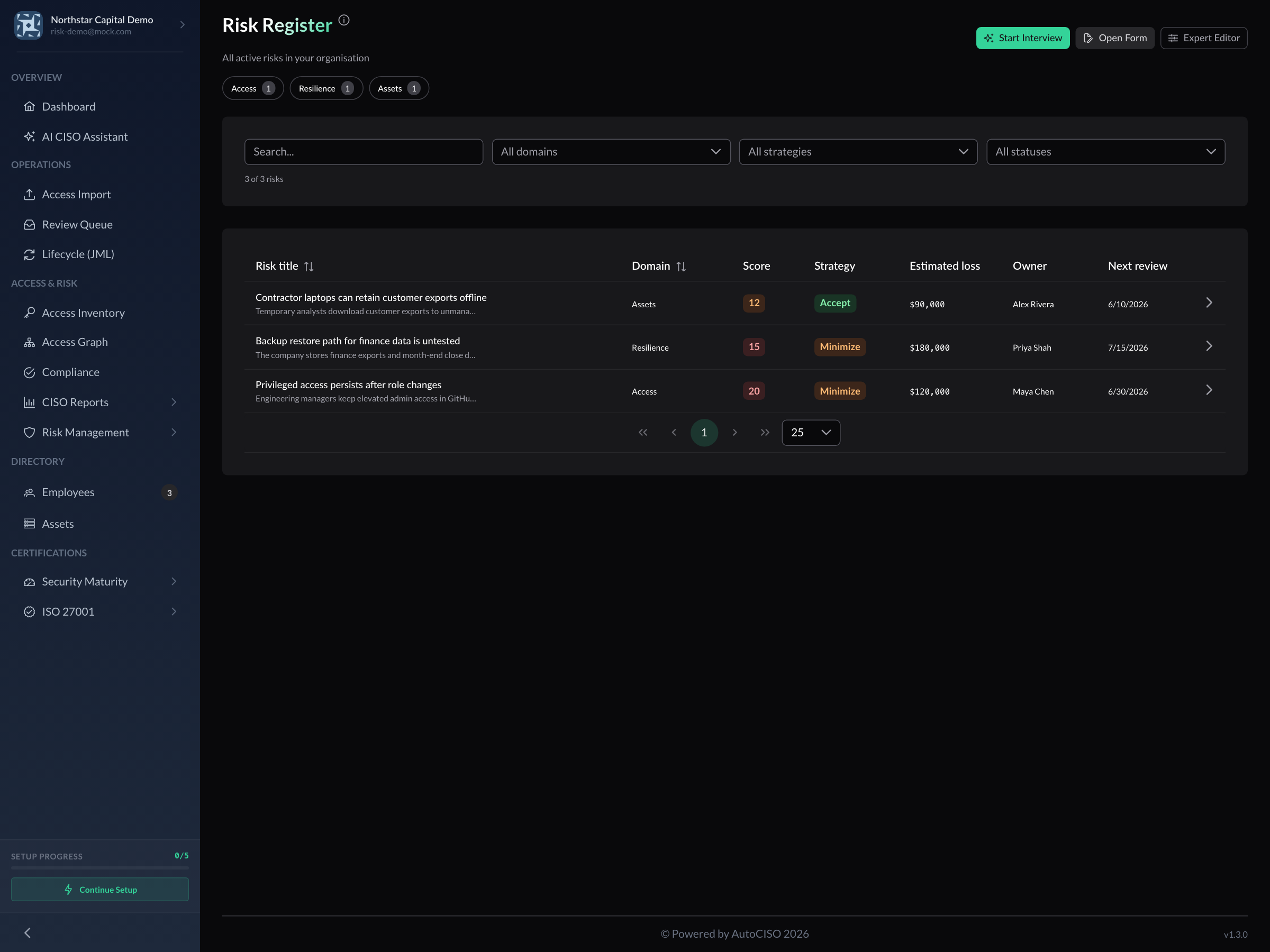
A live register becomes useful when it helps teams review, prioritise, and revisit risks instead of just store them.
This changes the conversation inside the business.
Instead of asking “do we have a risk register,” leadership can ask:
- What moved this month?
- What is still open?
- Which decision needs funding now?
- Which accepted risks should be challenged again?
That is a much better use of a risk program than producing a document auditors can admire once a year.
Treatment decisions should be budget-aware
Security teams often have enough information to argue that a risk matters. What they usually do not have is a clear way to connect treatment choices to the capital available.
That is where prioritisation turns political.
If two high risks both look serious, which one should be funded first? If a treatment plan reduces exposure but consumes a large part of the quarter’s operating budget, how should that be weighed against lower-cost controls elsewhere? If a team chooses to accept a risk temporarily, can they show that it was a conscious budget decision rather than passive drift?
These are not abstract framework questions. They are operating questions.
The Risk Budget view in AutoCISO puts active risks, estimated exposure, and budget allocation in the same place, so treatment choices can be defended in terms the business understands.
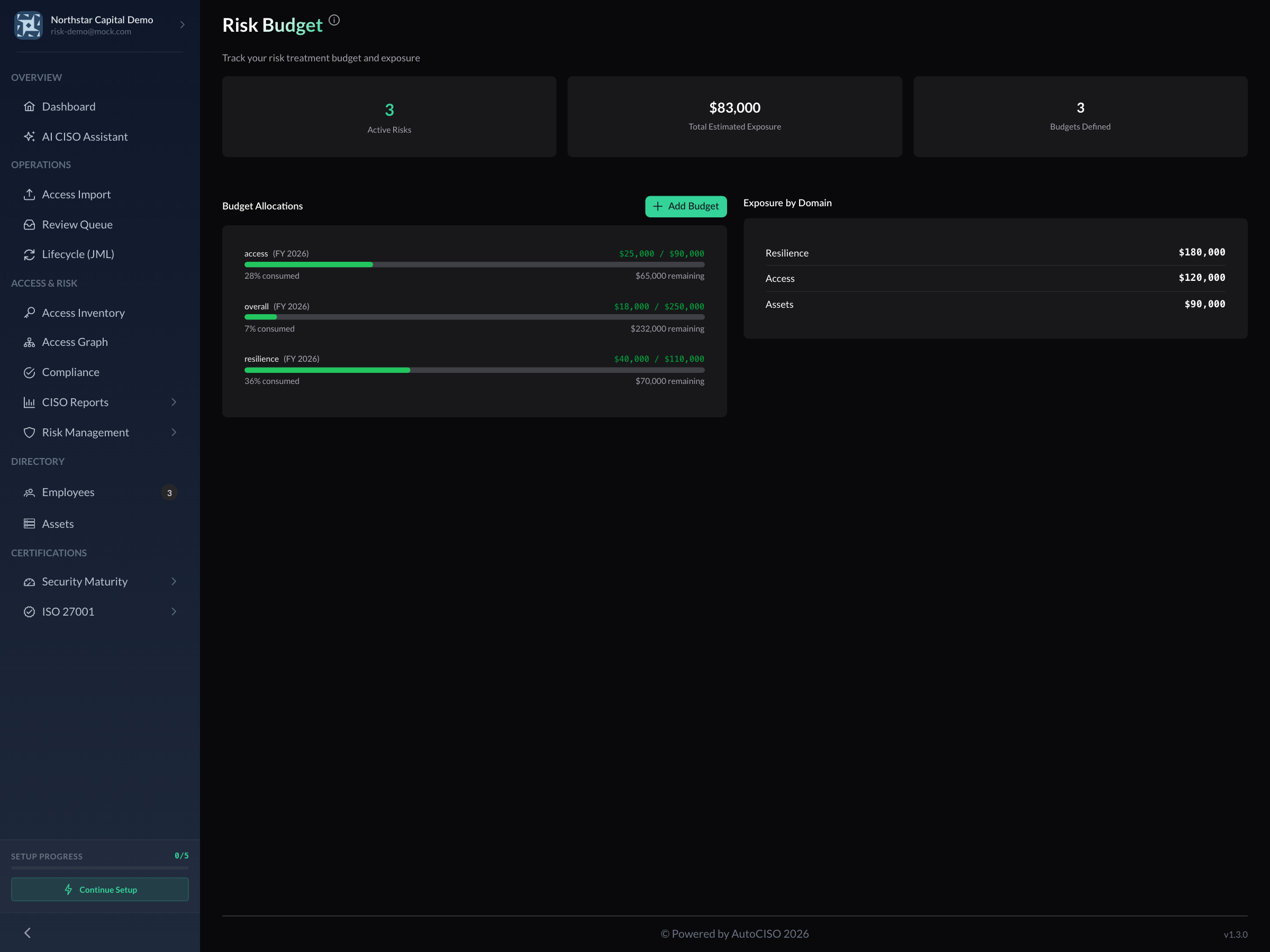
Budget context helps turn “this feels important” into “this is the next funded decision.”
That does not make risk decisions easy. It makes them explicit.
And explicit decisions are much easier to govern than implicit ones.
Why this matters to the business
For a security team, a better risk workspace means cleaner intake, more consistent records, and stronger review discipline.
For the business, it means something more important: the risk program becomes actionable.
That shows up in several ways.
Faster conversion from concern to tracked item. Operational stakeholders can start in a guided mode instead of waiting for a specialist to transcribe their issue into the register later.
Shared ownership. A risk can begin with one person’s concern and end with an accountable owner, a review date, and a selected treatment path in the same system.
Better prioritisation. Teams can compare estimated loss, selected strategy, and budget context in one place instead of juggling multiple documents.
Less spreadsheet drift. When the live product surface is also the place where decisions are reviewed, the register is far more likely to stay current.
That is the real value of better risk tooling: not prettier forms, but more durable decision-making.
Risk management should not depend on specialist patience
A growing company does not need a risk register because frameworks say it should.
It needs one because the business is now complex enough that important security and operational decisions cannot stay trapped in memory, side channels, and one-off workshops.
The hard part is not knowing that risk exists. The hard part is giving the organisation a workflow that people will actually use, update, and trust.
That is what the new Risk Management Workspace is for.
If you want the product view and the business case in one place, see the feature page here: