Most security teams do not have a scoring problem. They have a memory problem.
They can usually explain what feels broken right now. They can point to a few overdue actions, a noisy vendor review, a backlog of access cleanup, maybe the usual tension between shipping and hardening. What they cannot do, at least not quickly, is prove whether the program is actually getting better.
That is where manual spreadsheet hell starts. Every quarterly review turns into archaeology.
One vCISO we interviewed for our expert series put it bluntly: “My clients do not pay me to remember what happened in Q2. They pay me to tell them what matters now and what breaks next if they ignore it.”
A score on its own looks useful, but it still does not answer the question leadership actually cares about:
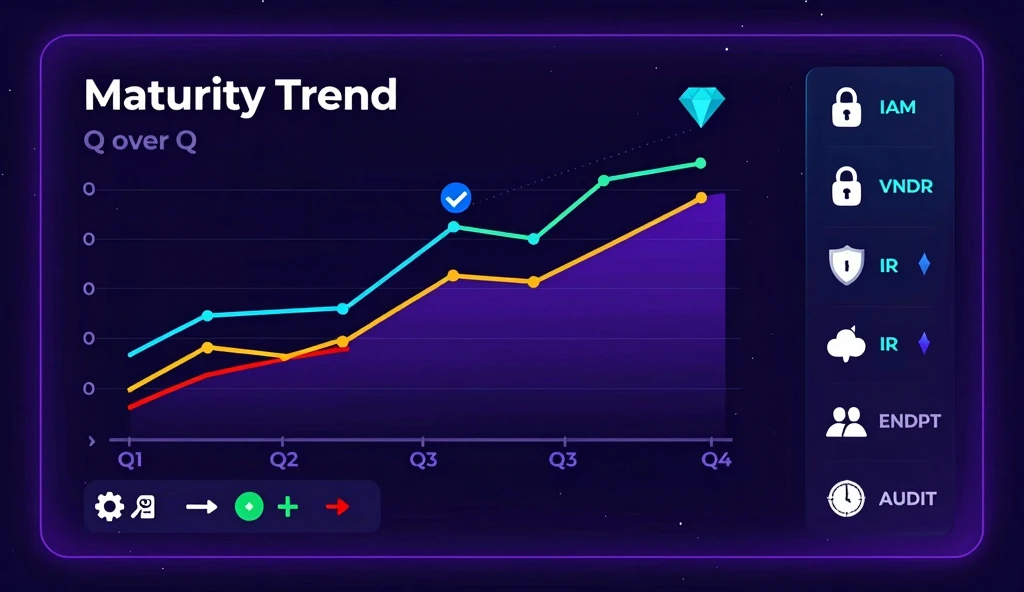
Are we getting better quarter after quarter, and why?
For a vCISO, that is the difference between strategy and storytelling. For a CEO or CTO, it is the difference between seeing progress and paying for narrative reconstruction.
A point-in-time assessment is not enough
In plain English, a maturity score is just a structured way to describe how reliably a security capability operates. Not whether a policy exists on paper, but whether the process actually works under normal pressure.
If a client scores 58 today, is that good or bad? On its own, you do not know.
You cannot know unless you also see:
- where it was last quarter
- which domains improved or degraded
- what actions influenced the change
- whether progress is fast enough for the company stage
Without that timeline, every review starts from zero. The vCISO has to reconstruct the story, and the client has to trust the interpretation without seeing the trend.
That is a bad operating model. It turns the advisor into an orchestra conductor with no sheet music, trying to keep tempo from memory while the board asks for confidence.
What the portal changes
When AutoCISO tracks maturity across quarters, the advisor can move from static status to an operating narrative.
Identity and access management, or IAM, is the discipline of controlling who gets access to what and when that access should be removed. It sounds administrative. In practice, it is where tribal knowledge, rushed onboarding, and weak offboarding quietly accumulate risk.
That is why trend matters more than a single snapshot. The vCISO can show what changed, why it changed, and what needs attention next:
- identity controls improved after the joiner/mover/leaver workflow was tightened
- third-party risk stalled because vendor reviews were started but not operationalized
- incident readiness improved after tabletop exercises and ownership changes
- endpoint visibility weakened after headcount growth outpaced IT processes
If access governance is flat for two quarters, that is a warning. If privileged access exceptions rise while headcount grows, that is a scaling problem. If vendor risk stays flat despite more tooling, that is an ownership problem.
The portal makes those patterns visible before they turn into audit pain, sales friction, or incident response. That is situational awareness, not dashboard decoration.
A realistic example
Consider a 250-person B2B software company with strong engineering talent and decent tooling. MFA is in place. Cloud infrastructure is not obviously broken. There is no recent incident. Leadership feels reasonably comfortable.
A fractional CISO starts tracking maturity by quarter instead of by anecdote.
Quarter 1 shows weak joiner/mover/leaver discipline and inconsistent access reviews. Quarter 2 shows some improvement, but identity governance barely moves because no one owns offboarding end to end. Quarter 3 shows privileged access exceptions rising again because the company hired quickly and tolerated shortcuts.
In a normal advisory model, those details are scattered across notes, spreadsheets, and memory. In a portal model, they show up as a clear health timeline.
Nothing here creates panic in a single monthly update. But over three quarters, the pattern is obvious: the company is scaling faster than its identity controls.
That is exactly the signal a CEO or CTO needs early, while fixes are still cheap. Security is a journey, not a destination, but it is still fair to ask whether the journey is moving in the right direction.
Why operators care about this
Most maturity tools stop at assessment. They tell you where you are standing. They do not help you explain the road behind you or the next turn ahead.
A vCISO Portal turns maturity into client-facing delivery.
1. Show progress in a language executives understand
Executives do not want raw controls. They want a credible answer to: are we reducing risk in the right areas, fast enough?
Instead of saying “things are improving,” the advisor can say:
- access governance improved for three straight quarters after process ownership moved to IT operations
- audit readiness increased after evidence collection was standardized
- vendor risk remains flat because procurement still operates outside the review process
That is board language, not security theater.
2. Link actions to outcomes
With a tracked timeline, the vCISO can connect recommendations to measurable movement:
- MFA expansion reduced identity exposure
- quarterly access reviews improved role hygiene
- better offboarding closed dormant-account risk faster
- control ownership reduced recurring audit exceptions
That is how an advisor proves the program is effective, not just active.
3. Catch stagnation before it becomes a bigger problem
If the score does not move for two or three periods, the problem is usually not budget. It is execution: weak ownership, manual process, or no operating discipline.
That is the moment a vCISO should intervene, and the portal gives them evidence to do it confidently.
That trade-off matters. Sometimes the right fix is expensive. Sometimes SCIM automation, which syncs user accounts and access changes between systems automatically, takes real budget and political effort. So do better IAM controls and clearer lifecycle ownership. A credible portal does not hide that. It makes the trade-off explicit so leadership can choose with open eyes.
Why this matters to the buyer
For the client, it means:
- clearer progress over time
- earlier visibility when risk stalls
- board-ready reporting tied to real operating data
- less dependence on one person remembering the whole story
For the vCISO, it means less manual reconstruction and a stronger portfolio story. It also changes the relationship with IT. Good IT is not there to block work. It is the invisible connector that helps people get access quickly, safely, and with less friction. When maturity trend is visible, conversations become less about nagging and more about trust-based decisions.
There is a reason major incidents keep forcing this lesson. NotPetya showed how operational weaknesses can turn into business-wide disruption, and the Midnight Blizzard intrusion reminded everyone that identity and access failures are rarely isolated technical details. The crown jewels are usually lost through ordinary process gaps that nobody tracked clearly enough over time.
Pragmatic roadmap
If you want maturity tracking to become operational instead of ceremonial, start here:
- Define 5-7 domains that matter to your business, not a giant framework nobody will maintain.
- Write down what “good enough this quarter” means for each domain in plain language.
- Capture a fixed snapshot every quarter and never rewrite history.
- Tie each score movement to one or two concrete operating changes.
- Review flat or declining areas first. That is where the real risk usually hides.
- Use the same timeline for board reporting, weekly advisory work, and remediation follow-up.
The best portal does not just show a number. It shows:
- historical movement across periods
- which domains improved or declined
- what activities likely influenced the trend
- where early intervention is needed
That is what turns maturity from a compliance artifact into a portfolio operating system. It is also the difference between classic GRC, where teams feed a checklist, and operational GRC, where security data changes what people do next.
If the score cannot drive ownership, prioritization, and follow-through, it is just another artifact. If it can, the portal stops being a reporting layer and becomes the working surface for the program.