The job posting said “mature security program.” The reality was 47 SaaS apps, a shared admin password in a Notion doc, and three former employees who still had active GitHub access six months after their last commit.
This isn’t unusual. It’s Tuesday.
What the First 90 Days Actually Look Like
Most security leaders joining a company at the CISO or VP Security level expect to spend their first weeks reviewing policies, meeting stakeholders, and conducting risk assessments. What they actually spend those weeks doing is building an inventory from scratch — because one doesn’t exist.
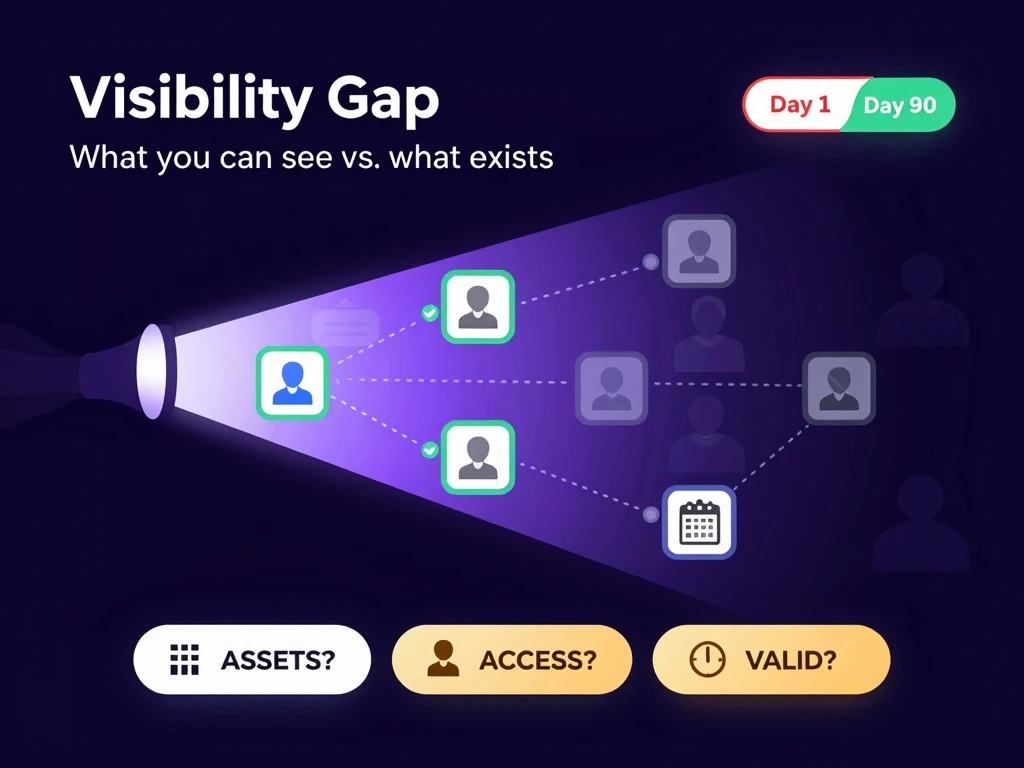
The foundational question — what do we have, who has access to it, and is that access still valid? — rarely has a clean answer. What exists instead is a patchwork: some apps managed by IT, some procured directly by department heads, some inherited from contractors who are long gone, and some nobody can quite remember signing up for.
This is the visibility gap, and it is where most security programs quietly fail before they ever get started.
You Cannot Protect What You Cannot See
The phrase gets repeated so often it has lost its urgency. But sit with it for a moment.
Every access review, every threat model, every compliance control assumes you have an accurate picture of your environment. If that picture is incomplete — and it almost always is — your entire security program is built on a foundation that is thinner than it looks.
Ghost accounts are the most obvious symptom. A terminated employee whose access was never fully revoked. A contractor whose project ended six months ago but whose credentials still work. A service account created for an integration that was replaced, then forgotten. These are not edge cases. In the average SMB audit, you find more than seven of them per application reviewed.
Ghost accounts are dangerous not because former employees are malicious — most aren’t — but because those credentials exist in credential dumps, phishing kits, and brute force lists. An account with no active owner has no one monitoring it for anomalous activity.
The Inventory Problem Is Harder Than It Looks
The natural response to all of this is “we need a better asset inventory.” True. But building one is harder than it sounds.
Enterprise tools like Okta, Azure AD, or SailPoint solve the inventory problem elegantly — if everything is connected to them. For the 90% of companies with fewer than 500 employees, most applications are not connected to a central identity provider. They have local accounts, SSO for some apps but not others, and legacy internal tools that predate SSO entirely.
You can spend months building a manual inventory and it will be out of date before you finish. Every new hire, every new tool adoption, every team that purchases a SaaS product without going through IT procurement widens the gap again.
What an Effective Visibility Strategy Actually Requires
The goal isn’t a perfect, static inventory — it’s a repeatable process for discovering what exists and who has access to it.
Start with what you can audit immediately. Every app has a user management screen. A directory listing with usernames, emails, roles, and login dates. You don’t need an API integration to read that. A screenshot is enough to start cross-referencing against your HR system.
Focus on departure risk first. Not all access risk is equal. Accounts belonging to people who have left the company are the highest-risk items in any environment. They are your quickest wins and your most defensible starting point with leadership.
Build evidence as you go. Every access review is a future compliance artifact. Audit trails, screenshots, cross-reference results — these are the evidence package your SOC2 or ISO 27001 auditor will ask for. Capture them from day one.
Treat visibility as a continuous process, not a project. The inventory you build this quarter will be stale next quarter. The goal is a cadence, not a document.
The Real Measure of Day Ninety
The question to answer by day ninety is not “do we have a security program?” It is: “can I tell the board exactly what we have, who has access to it, and how I know that list is current?”
If the answer is yes — even partially — you have built something more valuable than any policy framework or compliance certification. You have built visibility. Everything else in the security program is downstream from there.
The companies that get this right tend to share one trait: they stop treating access management as an IT project and start treating it as an ongoing operational discipline, with the same urgency and cadence as financial controls or legal compliance.
The ones that don’t tend to find out they should have when an auditor — or an incident — finds what they missed.